HTTPS

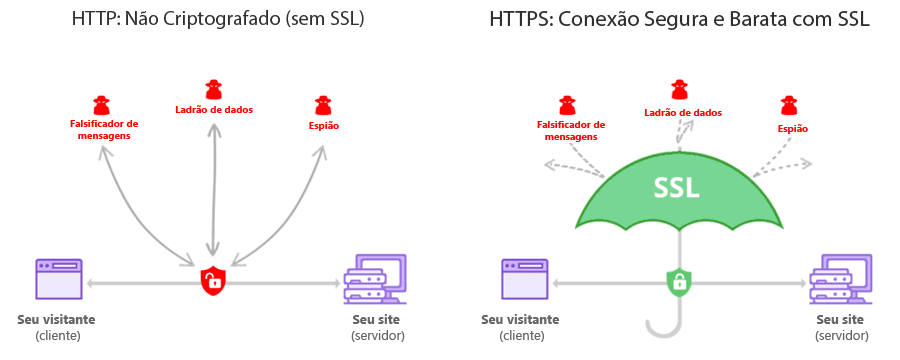
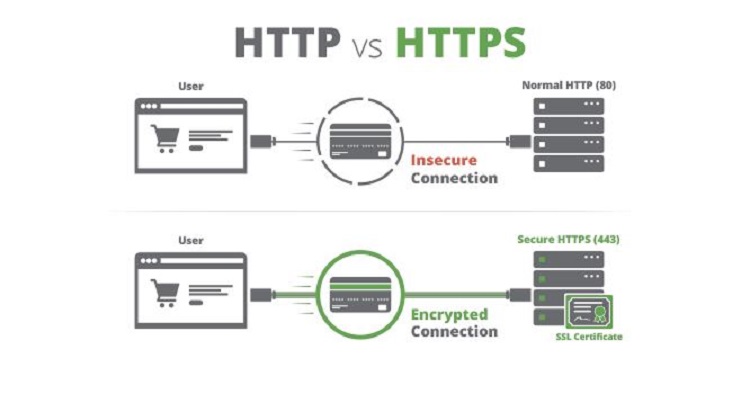
Refrain from all travel. I'm feeling secure about my place in the company. Because HTTPS piggybacks HTTP entirely on top of TLS, the entirety of the underlying HTTP protocol can be encrypted. The lowest level of local travel advisory, means that routine travel or activities may be restricted in areas because of a hazardous situation, and individuals should use caution or avoid those areas. Electronic Frontiers Foundation. Eckersley, Peter 2010-06-17. HTTPS should not be confused with the seldom-used S-HTTP specified in. from the original on 2018-10-20. from the original on 2019-04-24. He secured a loan using his house as collateral. Konigsburg, Eitan; Pant, Rajiv; Kvochko, Elena 2014-11-13. " The majority of web hosts and cloud providers now leverage Let's Encrypt, providing free certificates to their customers. from the original on 2017-12-02. sent reinforcements to secure their position Adjective We need to make our network more secure against attacks by hackers. We track this information using cookies, or small text files which include an anonymous unique identifier. It is used for over a , and is widely used on the Internet. The , opining that "In an ideal world, every web request could be defaulted to HTTPS", has provided an add-on called HTTPS Everywhere for , , , and , that enables HTTPS by default for hundreds of frequently used websites. A solution called SNI exists, which sends the hostname to the server before encrypting the connection, although many old browsers do not support this extension. , , and are interchangeable in many contexts where they indicate the making certain or inevitable of an outcome, but may imply a virtual guarantee the government has ensured the safety of the refugees , while sometimes stresses the taking of necessary measures beforehand careful planning should insure the success of the party , and distinctively implies the removal of doubt and suspense from a person's mind. The user trusts that the browser software correctly implements HTTPS with correctly pre-installed certificate authorities. Older browsers, when connecting to a site with an invalid certificate, would present the user with a asking whether they wanted to continue. It is recommended to use HSTS with HTTPS to protect users from man-in-the-middle attacks, especially. In May 2010, a research paper by researchers from and discovered that detailed sensitive user data can be inferred from side channels such as packet sizes. Even though about individual pages that a user visits might not be considered sensitive, when aggregated it can reveal a lot about the user and compromise the user's privacy. Additionally, on a site served through HTTPS must have the enabled. 0 boosters claim, all of this will be more secure and less expensive than the tools offered by the likes of Microsoft and Facebook. — Much of that secure and prosperous future will depend on the health and safety of our microchip industry. Web browsers are generally distributed with a list of so that they can verify certificates signed by them. Several websites, such as and , guarantee that they will always remain accessible by HTTP. from the original on 18 November 2019. Cooperate with public officials and disaster services forces in executing emergency operations plans. Our corporate packages are aimed specifically towards catering to enterprises that are awestruck by the complexities of security infrastructure and are in search of online security solutions that are the need of their business. Freedom of the Press Foundation. We also aggregate Non-Personal Information in order to track trends and analyze use patterns on the Site. — Some of the messages discussed how voting by mail is safe and secure and addressed early election results. from the original on 2018-10-08. The authority certifies that the certificate holder is the operator of the web server that presents it. An important property in this context is , which ensures that encrypted communications recorded in the past cannot be retrieved and decrypted should long-term secret keys or passwords be compromised in the future. We will notify you of significant changes to our Privacy Policy by placing a prominent notice on our site. Originally, HTTPS was used with the protocol. The mutual version requires the user to install a personal in the web browser for user authentication. from the original on 2019-12-13. During a "watch" local travel advisory, only essential travel, such as to and from work or in emergency situations, is recommended, and emergency action plans should be implemented by businesses, schools, government agencies, and other organizations. HTTP is not encrypted and thus is vulnerable to and , which can let attackers gain access to website accounts and sensitive information, and modify webpages to inject or advertisements. According to the , Let's Encrypt will make switching from HTTP to HTTPS "as easy as issuing one command, or clicking one button. Normally, the certificate contains the name and e-mail address of the authorized user and is automatically checked by the server on each connection to verify the user's identity, potentially without even requiring a password. In simple mode, authentication is only performed by the server. You are now entering a secure area. Looking for something a little more personal? from the original on 2018-10-31. The protocol is therefore also referred to as HTTP over TLS, or HTTP over SSL. I assure you that no harm will be done implies action taken to guard against attack or loss. The authentication aspect of HTTPS requires a trusted third party to sign server-side. A certificate may be revoked before it expires, for example because the secrecy of the private key has been compromised. Non-Personal Information In general, we use Non-Personal Information to help us improve the Service and customize the user experience. This includes the request URL which particular web page was requested , query parameters, headers, and cookies which often contain identifying information about the user. She scored a goal to secure the team's victory. From an architectural point of view:• — Democrats need to win both the elections to secure a majority in the Senate. The website provides a valid certificate, which means it was signed by a trusted authority. beginning with the HTTPS scheme and the domain name label The URI scheme HTTPS has identical usage syntax to the HTTP scheme. He believes his job is secure. They didn't begin to celebrate until they knew their victory was secure. — Drive-Thru Voting is a safe, secure and convenient way to vote. HTTPS creates a secure channel over an insecure network. Please specify correct verification characters. Most web browsers alert the user when visiting sites that have invalid security certificates. Pusep, Stanislaw 2008-07-31. [ ] For HTTPS to be effective, a site must be completely hosted over HTTPS. from the original on 2018-07-22. How We Protect Information We implement security measures designed to protect your information from unauthorized access. Traffic analysis attacks are a type of that relies on variations in the timing and size of traffic in order to infer properties about the encrypted traffic itself. , this front machine is not the application server and it has to decipher data, solutions have to be found to propagate user authentication information or certificate to the application server, which needs to know who is going to be connected. from the original on 2018-08-10. Therefore, a user should trust an HTTPS connection to a website all of the following are true:• Please specify verification characters. Please specify 6 verification characters. Changes To Our Privacy Policy The Company reserves the right to change this policy and our Terms of Service at any time. — Her inquiry began last year in March, after Michael D. In general, the Personal Information you provide to us is used to help us communicate with you or provide reasonable safeguards to verify identity. Verb We must secure the country's borders. In situations where encryption has to be propagated along chained servers, session timeOut management becomes extremely tricky to implement. Insecure networks, such as public access points, allow anyone on the same local network to and discover sensitive information not protected by HTTPS. The highest level of local travel advisory, means that travel may be restricted to emergency management workers only. Browser integration [ ] Most display a warning if they receive an invalid certificate. You should store your valuables in a secure place. In 2016, a campaign by the with the support of web browser developers led to the protocol becoming more prevalent. Obey and comply with the lawful directions of properly identified officers. from the original on 2013-07-17. Secure your belongings under the seat. However, these measures do not guarantee that your information will not be accessed, disclosed, altered or destroyed by breach of such firewalls and secure server software. Web browsers know how to trust HTTPS websites based on that come pre-installed in their software. Please update this article to reflect recent events or newly available information. Shuo Chen; Rui Wang; XiaoFeng Wang; Kehuan Zhang 2010-05-20. The reason given is: Out of date. This was historically an expensive operation, which meant fully authenticated HTTPS connections were usually found only on secured payment transaction services and other secured corporate information systems on the. The fact that most modern websites, including Google, Yahoo! Supercharged Protection Our Advanced Enterprise-Grade NextGen Firewall technology protects you from a myriad of threats lurking in the digital hemisphere and secures you online to a great extent. Hypertext Transfer Protocol Secure HTTPS is an extension of the HTTP. from the original on 2019-01-08. You can make your site secure with HTTPS Hypertext Transfer Protocol Secure [. Newer browsers also prominently display the site's security information in the. During a "warning" local travel advisory, individuals are directed to:• Support for SNI is available since 2, 8, 2. We further protect your information from potential security breaches by implementing certain technological security measures including encryption, firewalls and secure socket layer technology. 3, published in August 2018, dropped support for ciphers without forward secrecy. This is one reason why the and the Tor project started the development of , which is included in the Tor Browser Bundle. The attacker then communicates in clear with the client. This is the case with HTTP transactions over the Internet, where typically only the is authenticated by the client examining the server's. Newer versions of popular browsers such as , , and on implement the OCSP to verify that this is not the case. certificates are used to authenticate the server and sometimes the client as well. from the original on 2011-06-05. Additionally, some free-to-use and paid networks have been observed tampering with webpages by engaging in in order to serve their own ads on other websites. from the original on 2018-10-10. from the original on 2019-02-09. To do this, the site administrator typically creates a certificate for each user, which the user loads into their browser. On a site that has sensitive information on it, the user and the session will get exposed every time that site is accessed with HTTP instead of HTTPS. This certificate must be signed by a trusted for the web browser to accept it without warning. You should periodically check the Site and this privacy page for updates. — These example sentences are selected automatically from various online news sources to reflect current usage of the word 'secure. As SSL evolved into TLS , HTTPS was formally specified by in May 2000. It protects against , and the bidirectional of communications between a client and server protects the communications against and. Network Working Group May 2000. from the original on 2018-11-25. Grigorik, Ilya; Far, Pierre 2014-06-26. April 2019 An important property in this context is PFS. As a consequence, and are necessary to verify the relation between the certificate and its owner, as well as to generate, sign, and administer the validity of certificates. References [ ] from the original on 2015-03-01. Archived from 3 February 2019 on 15 February 2019. Save on , , , and more to keep your business organized, efficient and secure. com" and not some other entity. Additionally, many return a security warning when visiting prohibited websites. from the original on 2016-01-04. Guaay, Matthew 2017-09-21. Lawrence, Eric 2006-01-31. Main article: The security of HTTPS is that of the underlying TLS, which typically uses long-term and private keys to generate a short-term , which is then used to encrypt the data flow between the client and the server. Choose the Right Synonym for secure Verb , , , mean to make a thing or person sure. Google announced in February 2018 that its Chrome browser would mark HTTP sites as "Not Secure" after July 2018. HTTPS is now used more often by web users than the original non-secure HTTP, primarily to protect page authenticity on all types of websites; secure accounts; and to keep user communications, identity, and web browsing private. Limitations [ ] SSL Secure Sockets Layer and TLS Transport Layer Security encryption can be configured in two modes: simple and mutual. See also [ ]• The license plate number must be entered exactly as it appears on the. In practice, this provides a reasonable assurance that one is communicating with the intended website without interference from attackers. from the original on 2018-11-20. Google Webmaster Central Blog. — Hear us out: Paying with a smartphone is actually more secure and more efficient than using a credit card. Possessing one of the long-term asymmetric secret keys used to establish an HTTPS session should not make it easier to derive the short-term session key to then decrypt the conversation, even at a later time. org, but not the rest of the URL that a user is communicating with, along with the amount of data transferred and the duration of the communication, though not the content of the communication. from the original on 2018-06-20. from the original on 2018-10-17. The certificate correctly identifies the website e. This prompted the development of a countermeasure in HTTP called. from the original on 2018-11-14. from the original on 2018-10-19. Server setup [ ] To prepare a web server to accept HTTPS connections, the administrator must create a for the web server. In the past, this meant that it was not feasible to use with HTTPS. The principal motivations for HTTPS are of the accessed , and protection of the and of the exchanged data while in transit. DHE and key exchange ECDHE are in 2013 the only schemes known to have that property. If, for any reasons routing, traffic optimization, etc. A sophisticated type of called SSL stripping was presented at the 2009. A safe is provided to keep your valuables secure from potential thieves. This county isn't reporting any information at this time. The CA may also issue a to tell people that these certificates are revoked. Personal Information: We do not sell, trade, rent or otherwise share for marketing purposes your Personal Information with third parties. Please specify correct notice number. As more information is revealed about global and criminals stealing personal information, the use of HTTPS security on all websites is becoming increasingly important regardless of the type of Internet connection being used. HTTPS is also important for connections over the , as malicious Tor nodes could otherwise damage or alter the contents passing through them in an insecure fashion and inject malware into the connection. — How does the city ensure the voting machines are secure and reporting correctly? How We Use and Share Information• The browser sends the certificate's serial number to the certificate authority or its delegate via OCSP Online Certificate Status Protocol and the authority responds, telling the browser whether the certificate is still valid or not. — Recent Examples on the Web: Verb Then with 15 seconds to go Holland Woods swiped the ball from a Rams player at midcourt and went in for an uncontested layup to secure the outcome. — Johnson has little time left to secure a new trade deal with the European Union, but the United Kingdom faces a dire economic situation even if an agreement materializes. This practice can be exploited maliciously in many ways, such as by injecting onto webpages and stealing users' private information. PDF from the original on 2018-06-20. from the original on 2011-08-25. from the original on 2019-01-17. Please specify license plate number exactly as it appears on the notice. Myers, Michael; Ankney, Rich; Malpani, Ambarish; Galperin, Slava; Adams, Carlisle 1999-06-20. from the original on 2019-08-01. The Internet Engineering Task Force. HTTPS has been shown to be vulnerable to a range of attacks. , when the browser visits "", the received certificate is properly for "example. Choose from our selection of sassy or cool. Browse the latest personal check designs from , , , , , , and more. How secure is your front door? In HTTPS, the is encrypted using TLS or, formerly, Secure Sockets Layer SSL. With the exception of the possible cryptographic attack described in the section below, an attacker should at most be able to discover that a connection is taking place between two parties, along with their domain names and IP addresses. History [ ] created HTTPS in 1994 for its web browser. — For those who have already cast absentee ballots, a safe, secure and effective voting system ensures that their votes will be counted. In either case, the level of protection depends on the correctness of the of the software and the in use. — a secret anti-encryption program run by the US• The company has established a secure foothold in the market. Personal Information includes information you submit to us through either the contact us forms or through the payment on account process. from the original on 2018-11-18. Kerner, Sean Michael 2014-11-18. from the original on 2018-10-06. Newer browsers display a warning across the entire window. from the original on 2015-02-12. By using our Service, you acknowledge that you understand and agree to assume these risks. However, because website addresses and numbers are necessarily part of the underlying protocols, HTTPS cannot protect their disclosure. Please specify correct notice number and license plate number. HTTPS is designed to withstand such attacks and is considered secure against them with the exception of HTTPS implementations that use deprecated versions of SSL. Not all web servers provide forward secrecy. from the original on 2018-09-20. Recent Examples on the Web: Adjective The online courses include how to start a business, secure financing and develop a sales strategy.。 。 。
6